Today I noticed something strange. I am scripting with AzureAD PowerShell against Azure AD. I have created a script that will create a Service Principal Name with Directory Reader role. This worked perfectly in my old trial/demo tenant and in customer tenants.
Last week I had to recreate my test lab environment because the licenses expired (I use 1 year demo tenants). Today I tried to create the SPN with the previously created PowerShell script and add the Directory Reader Role.
That script errored out at the line:
Add-AzureADDirectoryRoleMember -ObjectId (Get-AzureADDirectoryRole | where-object {$_.DisplayName -eq “Directory Readers”}).Objectid -RefObjectId $sp.ObjectId
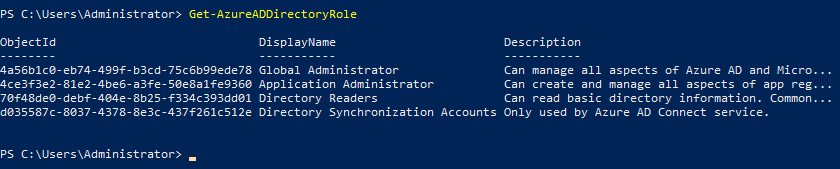
I tried logging in with Connect-AzureAD to the tenant in a new PowerShell window with my Global Admin account to the same tenant. After that I tried this command: Get-AzureADDirectoryRole
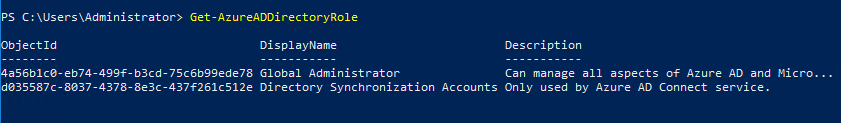
According to this PowerShell command there are only two Directory Roles.
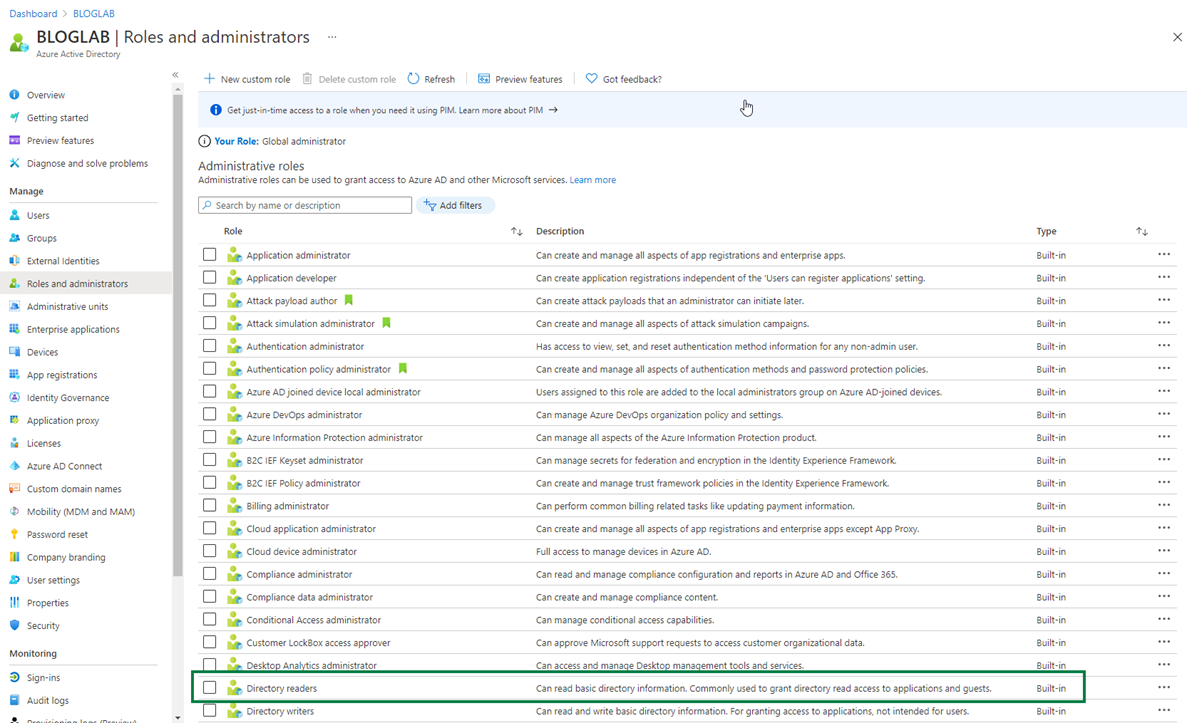 When I look in the Azure AD Portal, I see a lot more roles, including the Directory Reader I was looking for.
When I look in the Azure AD Portal, I see a lot more roles, including the Directory Reader I was looking for.
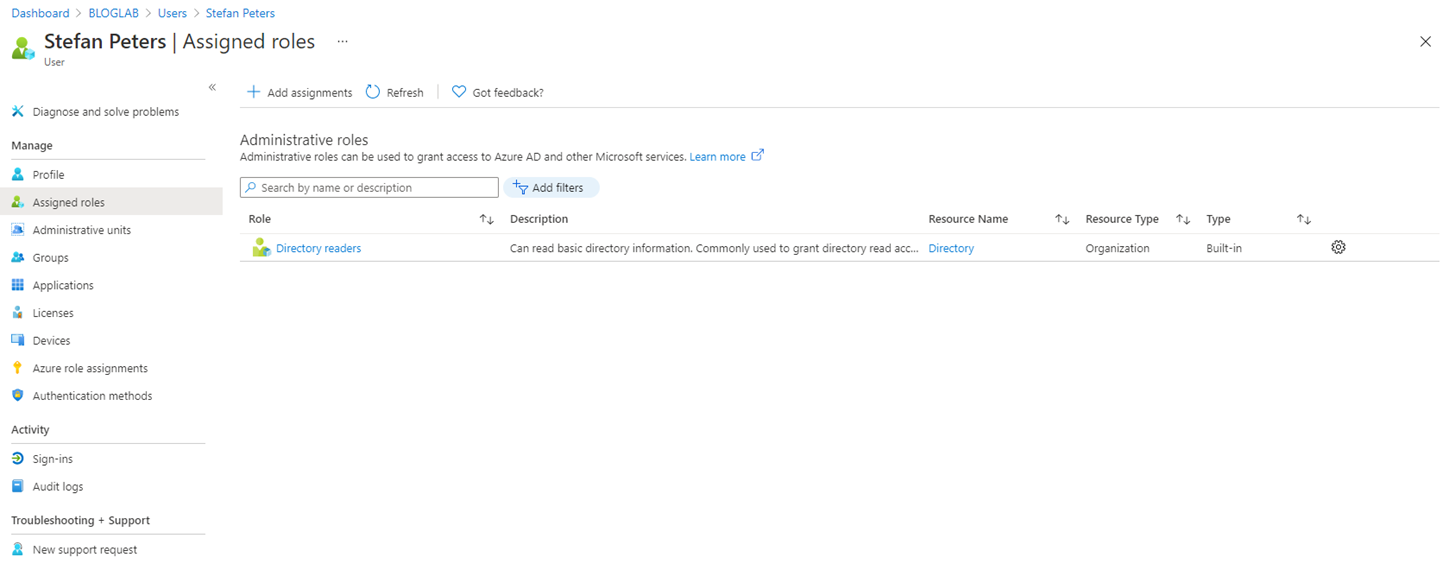 It is also possible to add this Role to a user.
It is also possible to add this Role to a user.
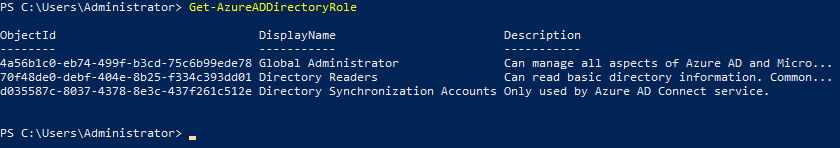
And very strange, after adding the Role to a user, the Role is also listed in the command: Get-AzureADDirectoryRole
Even after removing the Directory Reader role from the user again the PowerShell command keeps listing the Directory Reader role.
To prove this strange behavior, I added the “Application Administrator” to the same user and there it is.
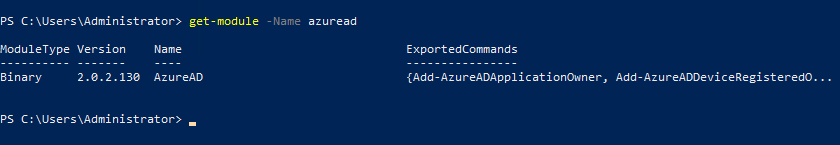
My AzureAD PowerShell modules is version: 2.0.2.130 at time of writing that is the latest version!
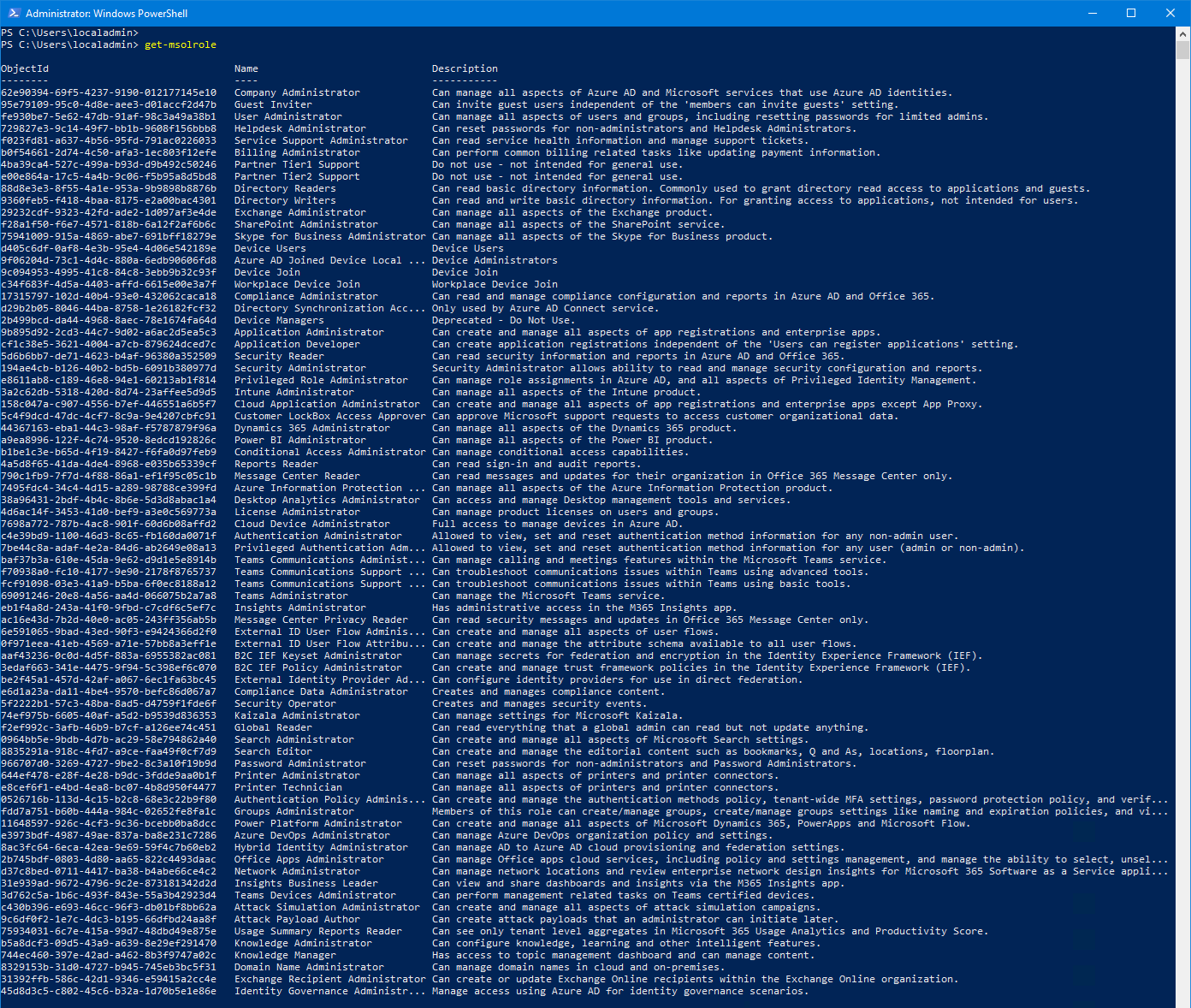 The old MSOnline PowerShell module with the Get-MSOLRole reveals all Roles as you can see above, that command was executed in the same tenant as the Get-AzureADDirectoryRole command.
The old MSOnline PowerShell module with the Get-MSOLRole reveals all Roles as you can see above, that command was executed in the same tenant as the Get-AzureADDirectoryRole command.
Conclusion:
At time of writing the Get-AzureADDirectoryRole command does not seem to be very reliable. You now know how to workaround this strange behavior. Just add the role to a user, and remove it afterwards to ‘activate’ the Role in AzureAD Powershell.